Blue Teaming3/29/2026
Beyond the Antivirus: Navigating the World of EDR and SIEM
In the modern cybersecurity landscape, simply "having security" isn't enough. As threats evolve, our tools must do more than just block known bad files. Today, I’m diving deep into my latest technical notes on the two pillars of a modern Security Operations Center (SOC): EDR and SIEM.
1. EDR: The Specialist on the Ground
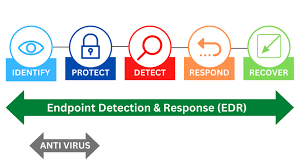 Endpoint Detection and Response (EDR) is a security solution designed specifically to monitor, detect, and respond to advanced threats at the endpoint level. In our world, an "endpoint" is any device—like a laptop or server—connected to an organization's network.
Endpoint Detection and Response (EDR) is a security solution designed specifically to monitor, detect, and respond to advanced threats at the endpoint level. In our world, an "endpoint" is any device—like a laptop or server—connected to an organization's network.
Why EDR? The "Airport Guard" Analogy
Think of a traditional Antivirus (AV) like an Airport Guard. The guard checks your passport against a database of known criminals; if you’re clean, you pass.
But what if a person has a clean record but plans to commit a crime after entering the airport? That is where the Security Team (EDR) comes in. They use CCTV and motion sensors to constantly monitor for suspicious activity, even if the person isn't on a "blacklist."
The Three Pillars of EDR
Visibility: Unlike firewalls, EDR provides impressive visibility into endpoint data, including process and registry modifications, file changes, and user actions, all presented in a complete timeline.
Detection: It goes beyond simple signatures to detect unusual behaviors using behavioral patterns and Machine Learning.
Response: EDR allows responders to take immediate action, such as isolating a host to prevent lateral movement, terminating malicious processes, or quarantining files.
2. SIEM: The Central Nervous System
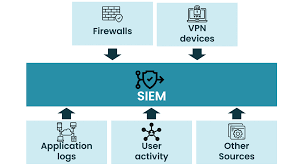 hile EDR is the expert on the ground, SIEM (Security Information and Event Management) is the brain that brings everything together.
hile EDR is the expert on the ground, SIEM (Security Information and Event Management) is the brain that brings everything together.
The Problem: Logs Everywhere
Every device on a network communicates and generates records called logs. These include:
Host-Centric Logs: Events happening inside the host, such as user authentication attempts or file access.
Network-Centric Logs: Communication between hosts, generated by firewalls, routers, or web traffic.
Without a SIEM, analyzing these is nearly impossible due to the sheer volume of data, lack of centralization, and limited context.
How SIEM Solves the Chaos
Centralization: It collects all host and network logs into one central place.
Normalization: It converts different log formats into a single, human-readable format.
Correlation: By linking individual logs together, it identifies a series of malicious events that might look harmless on their own.
Real-Time Alerting: It uses predefined rules to detect malicious activity and alert analysts instantly via a dashboard.
The Takeaway
Mastering these tools is about understanding Telemetry. Whether it's an EDR agent sending process data to a console or a SIEM ingesting logs via Syslog, the goal is the same: Visibility leads to Detection, and Detection leads to Response.
As I continue my journey toward May 2026, these foundations will be the core of my ability to defend complex networks.